AI at its core.
People where it counts.
Service Comparison
| Monitor Your Entire Digital Infrastructure Detect risks across your network, cloud platforms, endpoints, and applications. | ||||
| Machine Learning & User Behavior Analytics Real-time alerts driven by anomalous patterns in your data. | ||||
| SIEM Access and Visibility See all security log data in one centralized location with on-demand access to all retained logs. | ||||
| Instant Access to Security Experts Communicate around the clock with a US-based SOC team. | ||||
| Issue Triage and Guided Remediation Critical events, actionable, and response are delivered in ~ 8 minutes. | ||||
| SOAR Holistic threat management system through security orchestration and automated response. | ||||
| Threat Hunting Daily hunting for suspicious activity across all of your environments. | ||||
| Vulnerability Scanning Complete visibility of your networks and endpoints and their vulnerabilities. | ||||
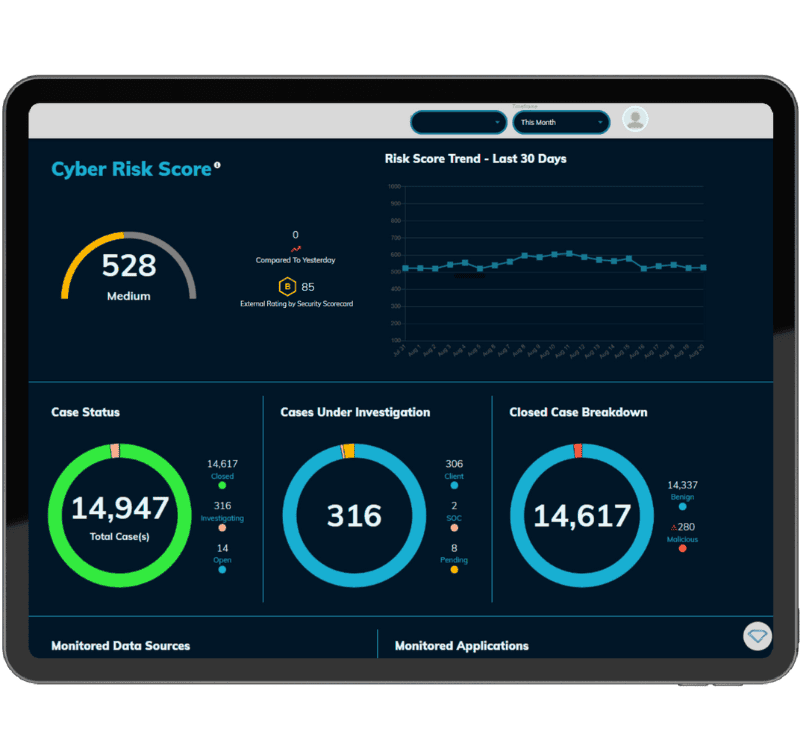
| Customized Reporting and Dashboards Automated and customizable KPI reporting and dashboards. | ||||
| Joint Install and Onboarding Support White-glove setup and integration to monitor and enhance existing security layers. | ||||
| Internal and External Cyber Risk Score Calculated by evaluating your entire landscape of your internal and external digital infrastructure. | ||||
| Compliance and Governance Track adherence to public and private sector security mandates (PCI, HIPAA, GDPR, NIST, NYDFS, etc.). |
Managed Endpoint Detection & Response (MEDR)
- Only covers endpoints, leaving vulnerabilities within the environment.
Managed Detection & Response (MDR)
- Limited by vendor and by levels of detection and response
for the entire environment.
Extended Detection & Response (EDR)
- Requires the people and processes of a SOC to operate.
Security Information and Event Management (SIEM)
- Collects security data, requires a SOC team to operate.
Strengths and Advantages
Customization
We don’t just watch for ‘normal’ industry threats. Our machine learning adapts to the behaviors of your specific cloud, network and users to create one-of-a-kind security operations center.
Relentless Monitoring
Our algorithms look for malicious threats, malware,
ransomware, and software vulnerabilities. Our 24 x 7 x 365 promise to you includes human-based responses, asset discovery, vulnerability assessment, intrusion detection, behavior monitoring, log management, and cloud-based SIEM.
ransomware, and software vulnerabilities. Our 24 x 7 x 365 promise to you includes human-based responses, asset discovery, vulnerability assessment, intrusion detection, behavior monitoring, log management, and cloud-based SIEM.
Customer Service
We’ll break down the info when you’re in a crisis, and in
between you’ll get consistent update meetings, one-on-one support, and quick access to real people when you need them.
between you’ll get consistent update meetings, one-on-one support, and quick access to real people when you need them.
Easy Integrations
- 2 week deployment time using a single agent across all endpoints
- Integrates with core threat vectors; Devices, Network, Cloud, Apps